As I’ve switched my home automation from Vera to SmartThings I’ve also been expanding my network of z-wave devices at home. Since SmartThings does such a great job with different notification options I’ve also been looking more into monitoring our home for different kinds of damage or danger. One of the first tasks on the agenda was to make our fire detection much smarter and able to alert us even if we are not at home. I looked around at the available market for z-wave smoke detectors and found a bit of a mixed bag. I could splurge and purchase the Nest device at roughly $100, or go with the Monoprice version of the Everspring Z-Wave Smoke Detector which runs at roughly $40.
However, after reading through the SmartThings forums a lot of people were having success using some of the devices which are certified for Lowe’s Iris Home Security and Automation system. The system runs z-wave as well and a lot of the devices are compatible with SmartThings since they both speak z-wave. First Alert makes a battery powered smoke detector with a model name of “ZSMOKE” which has built in z-wave and only costs $29.97. Note that they also make a CO2 z-wave model, however I already CO2 detection in the house, and I’m not as worried about being alerted to CO2 even when I’m away from the house. The other thing to know about CO2 detection is that the detection components deteriorate much quicker than they do for smoke alarms, which can lead to a lot of false alerts 4-6 years down the road.


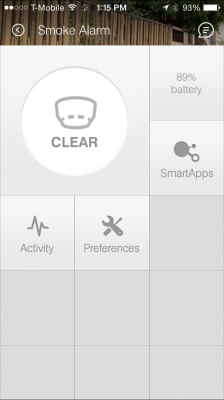
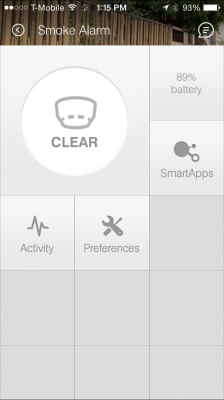
The smoke detector was easy to install into SmartThings (simply hold the test button as you insert the batteries to pair it to the system) and mount in an existing bracket on the ceiling. The smoke detector will continue to act as a regular (dumb) alarm until it is extended further on the SmartThings network with some SmartApps to go with it.
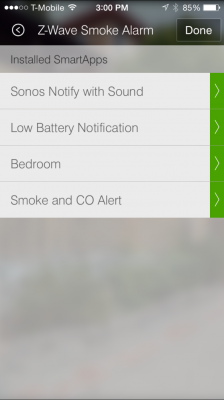
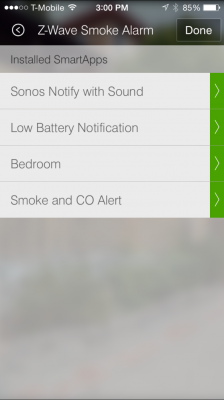
I’ve added several different SmartApps now that my SmartThings system has smoke detection:
Damage & Danger
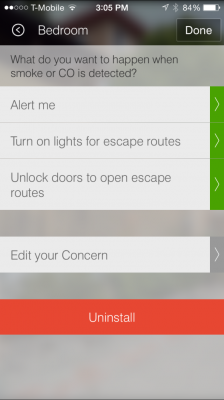
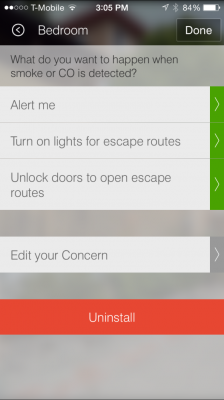
SmartThings has some out of the box SmartApps which are already configured for common scenarios with smoke detectors. There are several different options within these SmartApps, which all fall under the “Damage & Danger” category. Using these apps my SmartThings system will now do the following for any smoke alert:
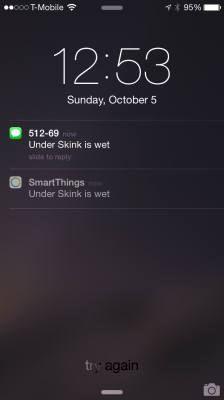
- Send an alert via the SmartThings app to our phones (when it triggers and when all clear)
- Send a text message for the smoke alert (when it triggers and when all clear)
- Turn on specific lights (most using GE z-wave switches)
- Unlock the front door (Kwikset SmartCode 914 Series Z-Wave Deadbolt which I’ll cover in a future post)
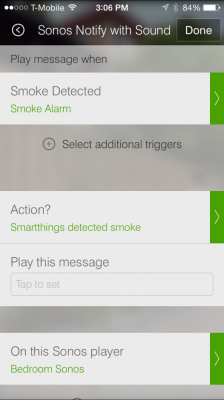
Sonos Notify With Sound
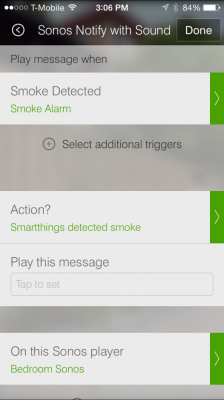
Sonos has some pretty cool integration options with SmartThings, some of which I’ll post further about in the future. For the smoke alarm, there is an app named “Sonos Notify With Sound” which will play a custom alert on any configured Sonos speakers when smoke is detected. This isn’t the most critical of features, as the smoke alarm is plenty loud, but generally I tend to think the more the merrier when it comes to fire alarms.
Low Battery Notification
SmartThings already has some low battery notifications built into the system, however there are other apps which people have created to select specific devices and battery levels and send an alert once they cross a specific threshold. I’ve installed one which I have configured to alert me when devices hit 10% battery.
Somethings with SmartThings are not always easy to setup and configure, but this was completely painless. The device works well and paired quickly, and SmartThings has most of the functionality needed in the SmartApps out of the box.
Save 10% on SmartThings
If you are interested in using SmartThings, this referral link will get you 10% off any shop.smartthings.com order containing a Hub or Kit.